Create a Secure and Unified Experience for Your Customers
Traditionally, Identity Access Management was a discipline for information security, by information security. No longer – today Identity enables your business. Our Customer Identity and Access Management practice understands this and will help you achieve your business goals with Identity as a foundation.
⦿ Get started with Digital Transformation (CIAM Advisory)
⦿ Build brand awareness by architecting SSO across your digital properties
⦿ Formalize CIAM by integrating your identity, marketing, and CRM platforms
⦿ Streamline external access to apps and APIs – quickly onboard users
⦿ Handle complete CIAM solution architecture
⦿ Protect high risk transactions and block malicious users
Most Importantly, we realize that you are not in the business of Identity. We partner with you so that your marketing, application, and information security teams focus their energies on what they do best. Let us provide the technical expertise and guidance so you can focus on your business goals.

Individual CIAM Services
Featured CIAM Solutions

Okta provides cloud software that helps companies manage and secure user authentication into applications, and for developers to build identity controls into applications, website web services and devices.

Ping Identity provides federated identity management and self-hosted identity access management and single sign-on solutions, providing standards to replace passwords for authenticating to web applications.
CUSTOMER IDENTITY AND ACCESS MANAGEMENT
Free CIAM Workshop
Learn what CIAM means, how vendors enable it, and the best way to start building a strategy for your organization
CIAM is a new and evolving area and sometimes before even starting an engagement it’s best to educate all stakeholders. We offer free workshops to provide our perspective on what customer identity access management means, what some of the common pitfalls are, and where would fit within your businesses. We will answer any questions you have and discuss potential engagements that may best fit your needs.
⦿ The importance of single sign-on (SSO), multi-factor authentication (MFA) to the customer experience
⦿ How CIAM can integrate with your CRM and Marketing tools
⦿ The pitfalls of legacy systems and how to avoid them

CUSTOMER IDENTITY AND ACCESS MANAGEMENT
CIAM Advisory
Evaluate your organization, workflow, and CIAM processes
Sometimes digital transformation is an executive driven goal. Other times, digital transformation naturally emerges from concurrent projects taking place across the enterprise. Regardless of why, you probably have questions about “how”. We bring the right people to the table and help you get your digital transformation program off the ground on the right foot.
⦿ Use Case Discovery and Analysis
⦿ Organizational Change Assistance
⦿ Architecture Guidance
⦿ Build vs. Buy and Vendor Considerations
CUSTOMER IDENTITY AND ACCESS MANAGEMENT
CIAM Architecture Services
Complete CIAM solution architecture and team training
You may have the best application teams in the world — when it comes to their applications. However, when trying to implement CIAM your internal developers may not be well versed on identity concepts and know where to begin – from implementing user journeys to selecting the right integration libraries to use. We can help by providing architecture guidance and input bringing disparate application teams to the table. We will coach your application teams on how best to integrate, cutting down on their development cycles and allowing them to return to focus on core business logic.
⦿ Handle complete CIAM solution architecture
⦿ Coach and enable application teams to integrate with CIAM tooling
⦿ Embed within sprint teams to ensure no disruption to the SDLC
⦿ Determine which processes need to be centralized in a CIAM solution vs. an existing applications in the organization

CUSTOMER IDENTITY AND ACCESS MANAGEMENT
CIAM Solution Deployment with Okta
Okta CIAM implementations can be complicated, but we can help
When Okta is used for CIAM, it becomes more complicated than traditional Okta deployments focused on your workforce. That is because Okta may become the trusted identity source, password tool, and integration hub for customers (something that would not happen for Employees). Our Okta Certified Developers assist with implementing Okta and integrating it with your business applications. We will suggest best practices based on our experience and walk you through various design tradeoffs that may arise.
⦿ Establish core customer profile
⦿ Define and implement user journeys
⦿ Enable SSO on all your applications
⦿ Integrate with CRM and Marketing Tools
⦿ Offer passwordless and 2FA to your customers
⦿ Migrate users from an existing application without disrupting access
CUSTOMER IDENTITY AND ACCESS MANAGEMENT
Implement API Access Management
We can help secure and monetize your API’s
CIAM does not just include making it easy for your customers to log in to business applications. As APIs expand and grow, their importance to business operations increases. We can help you implement an API access management solution such as Okta that ties together API and Identity, allowing you to both secure and monetize your API’s.
⦿ Modernize B2B Access Patterns and deprecate legacy integrations
⦿ Enable Client Self Registration
⦿ Monetize APIs
⦿ API Gateway Integration
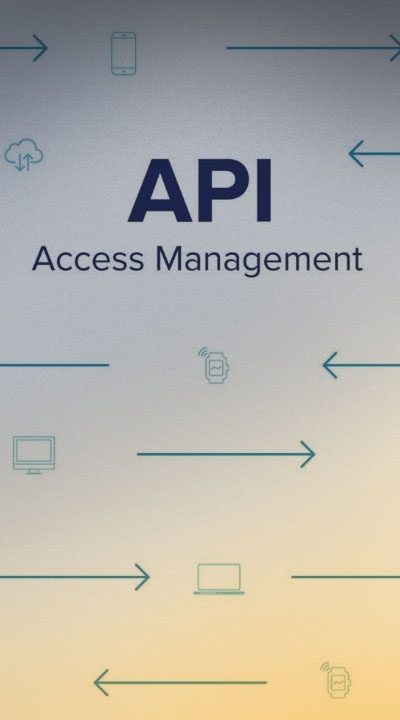
CUSTOMER IDENTITY AND ACCESS MANAGEMENT
Anti-Fraud and Identity Proofing
Protect your sensitive business transactions and identities
Digital transformation projects may expose sensitive business transactions to your external users. Modern CIAM solutions offer various identity proofing and anti-fraud integrations that you can use to provide a higher level of assurance that your users are who they say they are and have not been compromised. We can help provide architecture and implementation services so your organization can offer these high-value transactions without compromising security.
⦿ Centralize Customer Identity Security
⦿ Protect high-risk transactions
⦿ Block malicious users
⦿ Easily introduce 2FA as needed
CUSTOMER IDENTITY AND ACCESS MANAGEMENT
Implement Inbound Federation
Enable inbound federation to provide critical access to your external users
Your customers and business partners increasingly expect the ability to assert their identities outside of their organization. You need to be ready to allow them to “Bring Your Own Identity” (BYOI).
We can provide guidance and implementation services to enable inbound federation to your organization so you can provide critical access to your external users without having to manage their identities yourself. We can engage directly with your customers on your behalf to understand what their requirements are regarding federation or train your internal teams to have those discussions themselves.
⦿ Advise on what your customer expects for federation
⦿ Update your applications for BYOI
⦿ Engage directly with your customers if desired
⦿ Train internal support staff for BYOI onboarding

Why Integral Partners can help with Customer Identity and Access Management
We understand that CIAM projects can become much more complicated than traditional Okta deployments focused on your workforce. It’s much more than dealing with with simple SSO and MFA. We understand both the technical complexities and the processes that need to be considered when building a successful Identity program. We will work with your organization to understand what you want to accomplish and provide the expertise on how to achieve it.

Let’s talk about how we can help
Ready to learn more? Let’s start a conversation with one of our CIAM and Identity experts. They can answer any initial questions you have about our Customer Identity services and other IAM-related issues.
- We’re trusted partners with all leading vendors but tool-agnostic
- We have over 20 years of experience with IAM
- We can help with strategy, evaluation, purchase, implementation, and support
Use this form to reach out and get started.
